Remove Nanocrypt ransomware
Nanocrypt ransomware is file-encrypting malware. It’s a type of infection that takes users’ personal files hostage and demands payment for their recovery. When ransomware encrypts files, it adds an extension, which in this case is .ncrypt. Unfortunately, encrypted files will be unopenable unless they are first decrypted using a special decryptor. The only ones who have the decryptor are the ransomware operators, who will demand that you pay $50 for it. At the moment, only users who have backups can recover files for free.
When Nanocrypt ransomware is initiated, it immediately begins encrypting files. The main targets are personal files that users are likely to pay for, such as documents, photos, videos, and other images. Encrypted file titles will have the .ncrypt extension; for example, a text.txt file would become text.txt.ncrypt upon encryption. You will not be able to open any encrypted files unless you decrypt them first. However, acquiring the decryptor is not going to be easy as only the ransomware operators have it.
After encryption is finished, the ransomware generates a README.txt ransom note. This note informs victims that their files have been encrypted and outlines the steps to obtain a decryptor. Unfortunately, this decryptor is only available by paying a ransom of $50. While this amount might not seem like a lot, we don’t recommend you pay the ransom or even communicate with the ransomware operators.
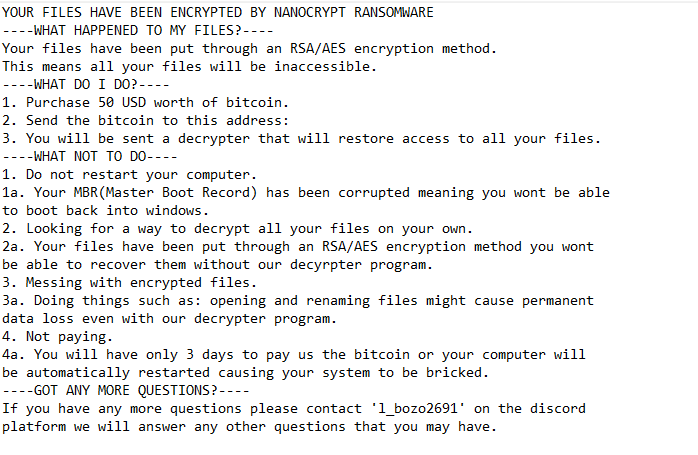
The ransom note dropped by Nanocrypt ransomware is below:
YOUR FILES HAVE BEEN ENCRYPTED BY NANOCRYPT RANSOMWARE
—-WHAT HAPPENED TO MY FILES?—-
Your files have been put through an RSA/AES encryption method. This means all your files will be inaccessible.
—-WHAT DO I DO?—-
1. Purchase 50 USD worth of bitcoin.
2. Send the bitcoin to this address:
3. You will be sent a decrypter that will restore access to all your files.
—-WHAT NOT TO DO—-
1. Do not restart your computer.
1a. Your MBR(Master Boot Record) has been corrupted meaning you wont be able to boot back into windows.
2. Looking for a way to decrypt all your files on your own.
2a. Your files have been put through an RSA/AES encryption method you wont be able to recover them without our decyrpter program.
3. Messing with encrypted files.
3a. Doing things such as: opening and renaming files might cause permanent data loss even with our decrypter program.
4. Not paying.
4a. You will have only 3 days to pay us the bitcoin or your computer will be automatically restarted causing your system to be bricked.
—-GOT ANY MORE QUESTIONS?—-
If you have any more questions please contact ‘l_bozo2691’ on the discord platform we will answer any other questions that you may have.
If you are considering paying the ransom, keep in mind that you are dealing with cybercriminals who have no obligation to help you. There’s no guarantee that a functional decryptor will be sent to you, or that you’ll receive any decryptor at all. Many people who have paid ransoms have discovered that the decryptors they received either didn’t work or were not sent at all.
If you have a backup, recovering your files should be relatively simple. You can access your backups and begin the recovery process as soon as you fully remove Nanocrypt ransomware from your system. Make sure to use an anti-malware program since ransomware is a complex infection. Once the ransomware has been removed, you can access your backups safely. Unfortunately, for those without backups, the best option is to save the encrypted files and hope that a free decryptor for Nanocrypt ransomware becomes available. However, there’s no guarantee that such a decryptor will ever be released.
How does ransomware infect computers?
Ransomware is often spread through various methods, including torrents, email attachments, and harmful links or advertisements. Users with poor online habits are at much higher risk of infection, as they often engage in riskier behaviors. To reduce the likelihood of malware infections, it’s a good idea to develop better browsing habits and to be aware of common ways that malware is distributed.
Emails are a widely used and convenient method for distributing malware. Cybercriminals frequently disguise malicious emails as notifications of parcel deliveries or order confirmations and claim that important documents are attached to the emails. This creates a false sense of urgency that compels users to open these attachments. However, these emails often contain obvious signs of being malicious. For example, they typically have noticeable grammar and spelling mistakes that you would not see in legitimate emails from reputable companies. Additionally, malicious emails often address recipients with generic words such as “User”, “Member”, or “Customer”, as malicious actors don’t have access to personal information about their targets.
When malicious actors target high-profile individuals or organizations, they often employ more sophisticated tactics, resulting in emails that look quite convincing. These emails might address the recipient by name and include details that give them credibility, making them appear more legitimate. Therefore, it is a good idea to refrain from opening unsolicited email attachments unless they have been scanned using anti-virus software or checked with VirusTotal.
Torrents are another common method for distributing malware. Because torrent sites are frequently poorly monitored, malicious actors can upload torrents that have malware. Users downloading torrents for movies, TV shows, or video games are particularly vulnerable to these threats. Not only is engaging in the piracy of copyrighted content illegal, but it’s also dangerous.
How to remove Nanocrypt ransomware
To successfully and safely remove Nanocrypt ransomware from your device, you have to use an anti-malware program. Attempting to remove the ransomware manually could lead to further damage to your system. After you fully remove Nanocrypt ransomware, you can connect to your backup to begin restoring your files. Remember, connecting to your backup while the ransomware is still active could result in the encryption of your backed-up files as well.
Site Disclaimer
WiperSoft.com is not sponsored, affiliated, linked to or owned by malware developers or distributors that are referred to in this article. The article does NOT endorse or promote malicious programs. The intention behind it is to present useful information that will help users to detect and eliminate malware from their computer by using WiperSoft and/or the manual removal guide.
The article should only be used for educational purposes. If you follow the instructions provided in the article, you agree to be bound by this disclaimer. We do not guarantee that the article will aid you in completely removing the malware from your PC. Malicious programs are constantly developing, which is why it is not always easy or possible to clean the computer by using only the manual removal guide.